Troubleshoot attack surface reduction rules
Applies to:
The first and most immediate way is to check locally, on a Windows device, which attack surface reduction rules are enabled (and their configuration) is by using the PowerShell cmdlets.
Here are a few other sources of information that Windows offers, to troubleshoot attack surface reduction rules' impact and operation.
When you use attack surface reduction rules you might run into issues, such as:
- A rule blocks a file, process, or performs some other action that it shouldn't (false positive); or
- A rule doesn't work as described, or doesn't block a file or process that it should (false negative).
There are four steps to troubleshooting these problems:
- Confirm prerequisites.
- Use audit mode to test the rule.
- Add exclusions for the specified rule (for false positives).
- Collect and submit support logs.
Confirm prerequisites
Attack surface reduction rules only work on devices with the following conditions:
- Devices are running Windows 10 Enterprise or later.
- Devices are using Microsoft Defender Antivirus as the sole antivirus protection app. Using any other antivirus app causes Microsoft Defender Antivirus to disable itself.
- Real-time protection is enabled.
- Audit mode isn't enabled. Use Group Policy to set the rule to
Disabled(value:0) as described in Enable attack surface reduction rules.
If these prerequisites are met, proceed to the next step to test the rule in audit mode.
Best practices when setting up attack surface reduction rules using Group Policy
When setting up the attack surface reduction rules by using Group Policy, here are a few best practices to avoid making common mistakes:
Make sure when adding the GUID for attack surface reduction rules, there are no double quotes (like this: "ASR Rules GUID") at the beginning or at the end of the GUID.
Make sure that there are no spaces at the beginning or at the end when adding the GUID for attack surface reduction rules.
Querying which rules are active
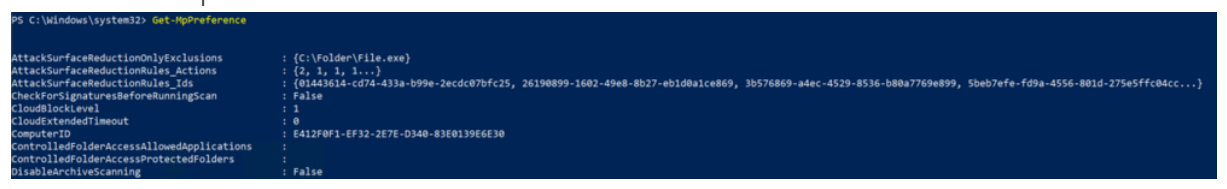
One of the easiest ways to determine if attack surface reduction rules are already enabled is through a PowerShell cmdlet, Get-MpPreference.
Here's an example:
There are multiple attack surface reduction rules active, with different configured actions.
To expand information on attack surface reduction rules, you can use the properties AttackSurfaceReductionRules_Ids and/or AttackSurfaceReductionRules_Actions.
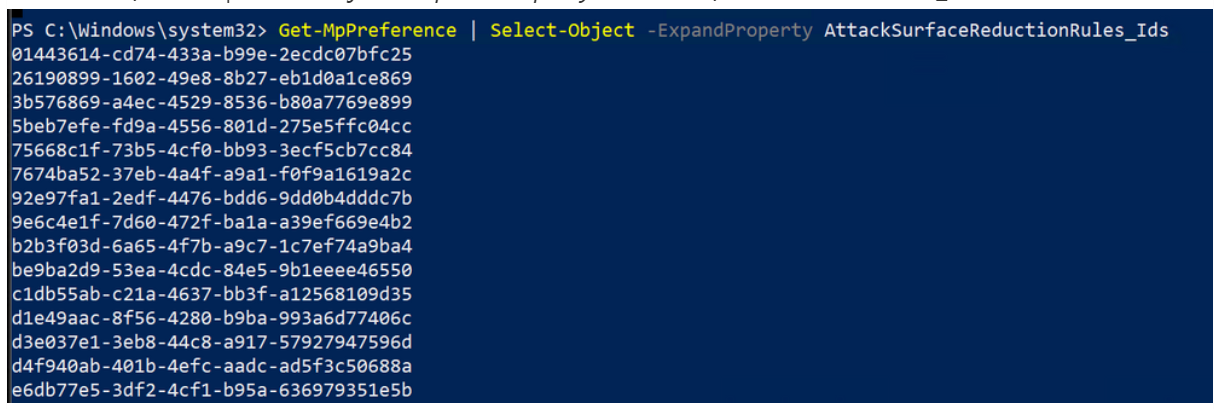
Example:
Get-MPPreference | Select-Object -ExpandProperty AttackSurfaceReductionRules_Ids
The preceding image shows all the IDs for attack surface reduction rules that have a setting different from 0 (Not Configured).
The next step is then to list the actual actions (Block or Audit) that each rule is configured with.
Get-MPPreference | Select-Object -ExpandProperty AttackSurfaceReductionRules_Actions
Use audit mode to test the rule
Follow these instructions in Use the demo tool to see how attack surface reduction rules work to test the specific rule you're encountering problems with.
Enable audit mode for the specific rule you want to test. Use Group Policy to set the rule to
Audit mode(value:2) as described in Enable attack surface reduction rules. Audit mode allows the rule to report the file or process, but allows it to run.Perform the activity that is causing an issue. For example, open the file or run the process that should be blocked, but is allowed.
Review the attack surface reduction rule event logs to see if the rule would block the file or process if the rule were set to
Enabled.
If a rule isn't blocking a file or process that you're expecting it should block, first check to see if audit mode is enabled. Audit mode might be enabled for testing another feature, or by an automated PowerShell script, and might not be disabled after the tests were completed.
If you tested the rule with the demo tool and with audit mode, and attack surface reduction rules are working on preconfigured scenarios, but the rule isn't working as expected, proceed to either of the following sections based on your situation:
- If the attack surface reduction rule is blocking something that it shouldn't block (also known as a false positive), you can first add an attack surface reduction rule exclusion.
- If the attack surface reduction rule isn't blocking something that it should block (also known as a false negative), you can proceed immediately to the last step, collecting diagnostic data and submitting the issue to us.
Querying blocking and auditing events
Attack surface reduction rule events can be viewed within the Windows Defender log.
To access it, open Windows Event Viewer, and browse to Applications and Services Logs > Microsoft > Windows > Windows Defender > Operational.
Add exclusions for a false positive
If the attack surface reduction rule is blocking something that it shouldn't block (also known as a false positive), you can add exclusions to prevent attack surface reduction rules from evaluating the excluded files or folders.
To add an exclusion, see Customize attack surface reduction.
Important
You can specify individual files and folders to be excluded, but you can't specify individual rules. This means any files or folders that are excluded from all ASR rules.
Report a false positive or false negative
Use the Microsoft Security Intelligence web-based submission form to report a false negative or false positive for network protection. With a Windows E5 subscription, you can also provide a link to any associated alert.
Collect Microsoft Defender Anti-malware Protection diagnostic data for file submissions
When you report a problem with attack surface reduction rules, you're asked to collect and submit diagnostic data for Microsoft support and engineering teams to help troubleshoot issues.
Open Command Prompt as an administrator and open the Windows Defender directory:
cd "c:\program files\Windows Defender"Run this command to generate the diagnostic logs:
mpcmdrun -getfilesBy default, they're saved to
C:\ProgramData\Microsoft\Windows Defender\Support\MpSupportFiles.cab. Attach the file to the submission form.
You can also view rule events through the Microsoft Defender Antivirus dedicated command-line tool, called *mpcmdrun.exe*, that can be used to manage and configure, and automate tasks if needed.
You can find this utility in %ProgramFiles%\Windows Defender\MpCmdRun.exe. You must run it from an elevated command prompt (that is, run as Admin).
To generate the support information, type MpCmdRun.exe -getfiles. After a while, several logs will be packaged into an archive (MpSupportFiles.cab) and made available at C:\ProgramData\Microsoft\Windows Defender\Support.
Extract that archive and you have many files available for troubleshooting purposes.
The most relevant files are as follows:
MPOperationalEvents.txt: This file contains same level of information found in Event Viewer for Windows Defender's Operational log.MPRegistry.txt: In this file you can analyze all the current Windows Defender configurations, from the moment, the support logs were captured.MPLog.txt: This log contains more verbose information about all the actions/operations of the Windows Defender.
Related articles
- Attack surface reduction rules
- Enable attack surface reduction rules
- Evaluate attack surface reduction rules
Tip
Do you want to learn more? Engage with the Microsoft Security community in our Tech Community: Microsoft Defender for Endpoint Tech Community.